Identity theft in trucking is not just a paperwork problem. It is often a load-security problem.
In freight, identity theft usually happens when someone uses another carrier’s identity, USDOT number, MC number, or business details without authorization, or when a bad actor presents itself as a legitimate carrier or broker in order to win freight, redirect loads, or get paid. FMCSA explicitly warns that broker and carrier fraud and identity theft occur when entities use another motor carrier’s assigned USDOT number without authorization or when someone acts as a broker without proper registration, and it states that fraud and identity theft are criminal acts.
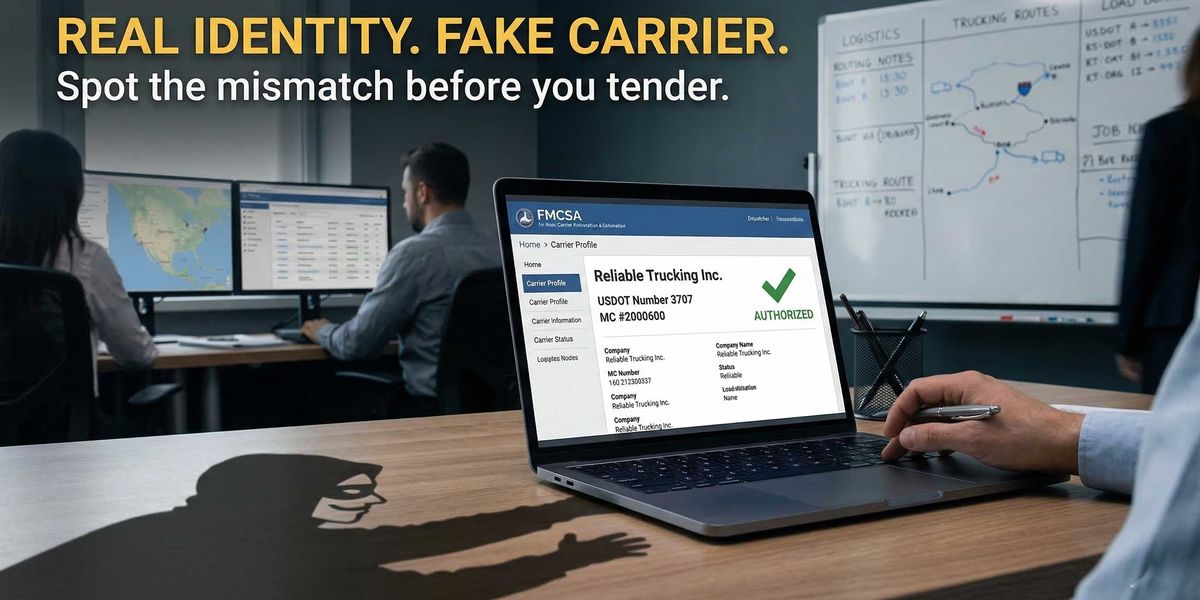
That is what makes trucking identity theft so dangerous: the company on the screen may not be the company you are actually dealing with.
A profile can look legitimate at first glance. The MC and DOT numbers may resolve. The company name may sound familiar. The paperwork may arrive quickly. But if the phone number, email domain, dispatch contact, authority story, or operating details do not line up, the risk is not theoretical. You may be handing a load to someone using a borrowed identity.
In this guide, we’ll cover:
-
what identity theft in trucking actually means
-
how it usually shows up
-
the biggest red flags to watch for
-
how to verify a carrier more carefully
-
what FMCSA checks can and cannot tell you
-
how to reduce the odds of getting burned
What is identity theft in trucking?
Identity theft in trucking happens when a person or company uses another carrier’s or broker’s identity without authorization in order to obtain loads, impersonate a legitimate business, misrepresent authority, or otherwise deceive another party in a freight transaction. FMCSA’s fraud guidance specifically describes fraud and identity theft as situations where entities use another motor carrier’s assigned USDOT number without authorization, or where someone acts as a broker without being properly registered with FMCSA.
At a practical level, that can look like:
-
using a real carrier’s DOT or MC number with different contact information
-
impersonating a legitimate carrier through email or phone
-
sending altered onboarding or insurance documents
-
posing as a broker or carrier under a real company’s identity
-
inserting a fake dispatch or booking contact into the process
The core problem is simple: the identity you verified may not belong to the party you are speaking with.
Why identity theft in trucking is so risky
Identity theft can create the same downstream problems that make freight fraud so expensive in the first place:
-
stolen or diverted freight
-
payment disputes
-
fake rate confirmations
-
confusion about who is actually hauling the load
-
insurance problems
-
delayed recovery when something goes wrong
-
reputational damage with customers and partners
FMCSA has publicly framed broker and carrier fraud and identity theft as active fraud concerns, and its fraud alerts page continues to publish warnings about phishing attempts, fake notices, and suspicious communications targeting motor carriers and others in the industry.
The damage often starts before pickup. Once a bad actor gets through onboarding or booking under someone else’s identity, your team may not realize there is a problem until the freight is already moving, missing, or unrecoverable.
How identity theft usually works
Most trucking identity theft schemes exploit one of three gaps:
1. A real company identity gets borrowed
The scammer uses a legitimate carrier’s or broker’s name, DOT number, MC number, or public profile information to look credible.
2. The contact layer gets swapped
The public identity may be real, but the phone number, email address, dispatch contact, or onboarding instructions belong to someone else.
3. The workflow moves too fast
A load gets tendered before anyone fully verifies that the company booking the freight is the same company tied to the authority, insurance, and operational footprint.
That is why a simple “does this MC number exist?” check is not enough. In many identity-theft cases, the stolen identity belongs to a real company.
Common signs of identity theft in trucking
Identity theft rarely announces itself clearly. It usually shows up in small mismatches.
Here are some of the most common red flags.
1. The DOT or MC number resolves, but the contact details do not match
This is one of the biggest warning signs.
A carrier may provide a real USDOT or MC number, but the phone number, email address, or dispatch contact does not match what you would expect from the legitimate company behind that record. FMCSA specifically warns about entities using another motor carrier’s assigned USDOT number without authorization.
If the identity is real but the communication layer is different, stop and verify before moving forward.
2. The email domain feels off
Be cautious when:
-
the email uses a free consumer domain when the company claims to be established
-
the domain is misspelled or slightly altered
-
the company name and email domain do not line up
-
different people in the same thread use different domains or signatures
Identity theft often hides in the contact surface, not the authority record.
3. The company is unusually eager to book immediately
Fraudsters often need speed.
Be careful when a carrier or dispatch contact:
-
pushes aggressively for immediate tender
-
avoids detailed operational questions
-
wants the rate confirmation before normal verification is complete
-
changes the point of contact during the process
-
becomes evasive when asked who is actually hauling the load
Urgency is not proof of fraud, but it is often part of the pattern.
4. Documents look legitimate, but the story does not hold together
A fake identity does not always come with obviously fake paperwork.
Sometimes the documents are polished. The issue is that they do not line up cleanly with the public record, the company’s operating story, or the people communicating with you.
Watch for:
-
inconsistent company names
-
mismatched addresses
-
different phone numbers across forms
-
signatures that do not match the stated company
-
certificates and onboarding documents sent from unrelated contacts
5. The authority story does not match the role being played
FMCSA directs users to check the Licensing & Insurance system to confirm authority status, and its FAQ specifically instructs users to review the “Authority Status” section there.
That matters because a frequent fraud pattern is not just stolen identity — it is misrepresented role.
If the company is acting like a broker but presenting itself as a carrier, or if the authority history does not make sense for the story you are being told, that deserves escalation.
6. The company profile looks clean, but very thin
SAFER’s Company Snapshot is useful, but FMCSA describes it as a concise record of identification, size, cargo, inspection and out-of-service summary, crash data, and safety rating if any. FMCSA also notes that inspection and crash counts on the snapshot reflect the previous 24 months, not an entire lifetime history.
That means a clean-looking profile can still be thin.
A company with little operating history, very recent authority, few inspections, and limited visible footprint may be legitimate — but it may also be easier for a bad actor to imitate or misuse in a booking workflow.
7. Several small inconsistencies appear together
This is where teams get into trouble.
Any one of these issues may be explainable:
-
a different phone number
-
a last-minute contact change
-
an unusual email domain
-
vague answers about dispatch
-
thin profile history
-
odd urgency
But when several appear together, the right move is not to rationalize them away. It is to pause and verify.
How to prevent identity theft from slipping through your carrier vetting process
Step 1: Verify the legal identity basics
Start with the core record:
-
legal company name
-
USDOT number
-
MC number
-
authority status
-
insurance filing status
FMCSA directs users to SAFER for the company snapshot and to Licensing & Insurance for licensing and insurance status checks.
Do not stop at “the number exists.” Confirm that the identity details actually fit together.
Step 2: Verify the contact layer separately
This is where many fraud checks fail.
Confirm:
-
the dispatch phone number
-
the email domain
-
the sender’s signature
-
whether the contact appears tied to the actual company
-
whether the communication details remain consistent across the process
A legitimate public record paired with illegitimate contact details is one of the clearest identity-theft patterns in trucking.
Step 3: Make sure the company’s role matches its authority
A key question is not just who are you, but what role are you legally claiming to play?
Review whether the party is presenting itself as:
-
the motor carrier hauling the load
-
a broker arranging transportation
-
some other intermediary
If the authority and role do not line up, that is a major warning sign. FMCSA’s public fraud guidance specifically includes situations where someone acts as a broker without proper registration.
Step 4: Pressure-test the operating story
Ask whether the company’s operational claims make sense.
For example:
-
Does the equipment story fit the load?
-
Does the lane make sense?
-
Does the fleet size match the claims being made?
-
Does the dispatch setup seem credible?
-
Can the company clearly explain who is picking up and hauling the freight?
Identity theft gets through when teams verify documents but never challenge the operating narrative.
Step 5: Slow the workflow down when something feels off
Fraud depends on momentum.
A good process should make it harder for a bad actor to exploit speed. That means requiring verification before tender, not after.
If something changes midstream — a new phone number, a different email address, a rushed request for immediate setup, a different company name on documents — treat the change itself as a signal.
Step 6: Escalate before tendering, not after pickup
Once the load is already moving, your options get worse.
If the identity story is weak, hold the load until someone on your team can verify:
-
the company identity
-
the contact information
-
the authority status
-
the insurance context
-
the hauling party
The time to stop identity theft is before freight is released.
A practical identity-theft checklist for trucking teams
Before booking or tendering, ask:
-
Did I verify the USDOT and MC numbers?
-
Did I confirm the authority status fits the role being claimed?
-
Did I check SAFER and Licensing & Insurance rather than relying on one screen alone?
-
Do the phone number, email domain, company name, and dispatch contact all match?
-
Does the operating story make sense for this carrier?
-
Do the documents line up with the public record?
-
Has anything changed during the booking process?
-
Are there multiple small inconsistencies that should trigger escalation?
If several of those answers are weak, unclear, or inconsistent, do not rely on the fact that the company “looks real.” That is exactly how identity theft gets through.
What FMCSA checks can tell you — and what they cannot
FMCSA’s public systems are essential for checking whether a company exists, what authority it has, and what parts of its public record are visible through SAFER and Licensing & Insurance. SAFER provides a concise snapshot record, while Licensing & Insurance is the official public place to review authority status and related filing information.
But those systems do not automatically answer every question that matters in an identity-theft scenario.
They may not fully tell you:
-
whether the person emailing you is actually tied to the company
-
whether the dispatch contact is legitimate
-
whether a real company’s identity is being borrowed
-
whether the operational story is credible
-
whether the party booking the freight is the party actually hauling it
That is why identity theft in trucking is not just a data problem. It is a verification process problem.
What to do if you suspect identity theft
FMCSA says that if you suspect your company has been the victim of fraud or identity theft, you should avoid suspicious links, use trusted channels, and report scams or suspicious communications. FMCSA’s fraud alerts page also points users to CISA for phishing guidance, to the FTC for scam reporting, and in some cases to the FBI’s Internet Crime Complaint Center, local law enforcement, or a state attorney general’s office. FMCSA also provides complaint pathways through the National Consumer Complaint Database and related complaint resources.
Practically, that means:
-
stop the transaction if possible
-
verify the real company through known-good channels
-
preserve emails, phone numbers, documents, and timestamps
-
report the issue through the appropriate FMCSA and law-enforcement channels
-
review whether the load, payment, or onboarding workflow was exposed
The faster you act, the better your odds of limiting damage.
The biggest mistake teams make
The biggest mistake is assuming that a real MC or DOT number means the person on the other end is real too.
That is not how identity theft works.
In many cases, the record is real. The company is real. The identity being borrowed is real.
The problem is that the contact, control, or transaction layer is fake.
If your process only checks that the carrier exists, but not that the booking contact truly belongs to that carrier, you are leaving the most important gap open.
How AlphaLoop helps
Identity theft is harder to catch when your team is forced to rely on a thin public record and a fast-moving booking workflow.
AlphaLoop helps teams go beyond surface-level carrier checks by adding more context around:
-
carrier identity
-
authority review
-
contact consistency
-
operational credibility
-
related-entity signals
-
risk indicators that do not show up clearly in a basic public snapshot
The goal is not just to confirm that a company exists.
It is to confirm that the company you are dealing with is actually the company you think it is.